If you’ve been frantically googling “Why is my WP site redirecting my users to another website?” you’re most likely a victim of WordPress Redirect Hacking, one of the many innovative hacking methods hackers deploy. To understand this better, you need to understand how WordPress-targeting hackers work. In this article, we’ll also tell you how it impacts your online business, and how you can fix this. Let’s get started.
Signs of a WordPress Hacked Redirect
First of all, let’s understand if your site is showing any of the following signs –
- Your website is redirecting its users to another website.
- Your administrator sees the “404 Error” page after signing into the dashboard.
- Your website is marked as “spam” or “hacked” on Google search results.
- Your website shows multiple push notifications that were not created by you.
- You are unable to sign in to your account’s admin panel or access the dashboard.
- There is some malicious or unidentified code in the .htaccess or index.php file of your WP installation.
If your answers to any of the above were yes, then you have been compromised with a hacked redirect attack. Each of these issues can be severely damaging to your business. Let us see how in the next section.
How WordPress Redirects Can Impact Your Business
Here are some ways in which redirects attacks can impact your business:
- Your website visitors are redirected to unsolicited external websites, causing an immediate loss of traffic that can affect business revenue – particularly if you are running an eCommerce store.
- Even a single redirect could lead to online users losing their trust in your brand and reputation – and are less likely to revisit your website.
- Loss of SEO ranking as Google could suspend or even blacklist your website; this can further lead to incoming traffic loss.
- Your website could also be suspended by your WordPress hosting company.
- Your administrator can no longer access the Admin dashboard page or perform any admin tasks.
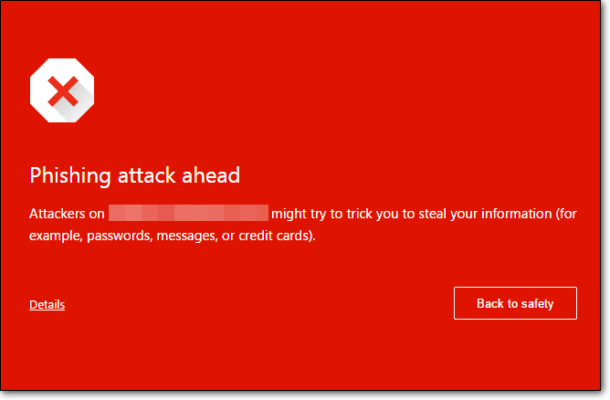
- Your redirected visitors could end up sharing personal or confidential information on the external phishing website – because of which hackers could misuse the data to make money or carry out unauthorized transactions.
- Finally, hackers now have a way to infect your website again – even after cleaning and fixing the problem.
These are just a few ways in which a redirect attack can compromise your website and business. So, how can you detect and fix your website following a redirect attack? Let’s find out.
How to Clean Your Hacked Website from Hacked Redirect
To clean and fix your website from the Hacked Redirect infection, you can use either of the following methods:
- Automatic malware cleanup: that uses a plugin or tool for malware scanning and cleaning.
- Manual malware cleanup: that is the technical way of site cleanup.
Let us discuss each of these methods, and determine which is more effective and easier to use.
Method 1 – Automatic Malware Cleanup
Thanks to its global popularity, WordPress has several security plugins or tools that you can easily install and use to detect and remove any malware like Malicious redirects, SEO Spam, Link Injection and more. One of the most popular ones is MalCare.
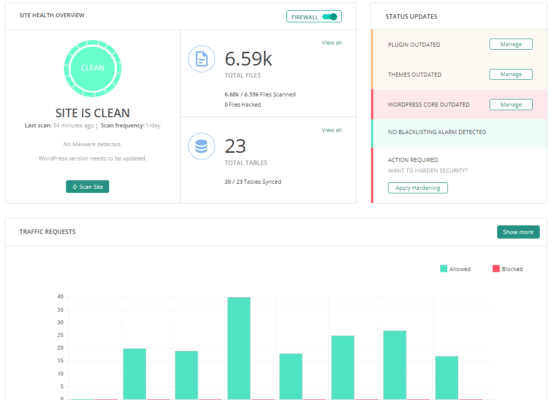
Apart from being effective against different types of malware infections, it is fast, user-friendly, and can detect and remove malware instantly. While there are many paid security tools, we recommend MalCare because, from our experience, it offers a one-stop solution for malware scanning and removal. Here is how you can use MalCare:
- Download and install the MalCare plugin for your website.
- After installation and activation, the tool automatically performs a complete scan of your site.
- From the Security panel in the dashboard, view if there are any hacked files.
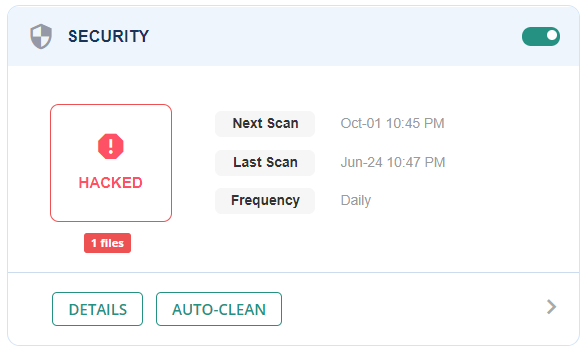
- Next, click the “Auto Clean” button in the Security panel.
That is all you need to do – MalCare will clean your website from any infections or malicious code.
Finally, to protect your website from future attacks, navigate to the “Website Hardening” section and click “Apply Hardening.”

Apart from easy scanning and cleanups, the security plugin offers a range of other security features that makes it worth your money.
If you are not keen to invest in a paid tool, you can opt for manual scanning and removal. Let’s discuss this in the next section.
Method 2 – Manual Malware Cleanup
Before we go ahead, it’s important to remember that manual malware cleanups are a challenge even for seasoned users – plus, it is time-consuming and involves a few technical steps. We would only recommend you use this method if you are confident of tech and WordPress knowledge and skills.
Before performing a manual cleanup, we recommend taking a complete backup of your website and database. You can use a backup plugin like BlogVault that automates database backups and stores your files securely in an independent location.
Once that’s done, follow the below steps for manual cleanup:
- Your Core WP files are most likely to be targeted by hackers. Don’t forget to check them which include wp-config.php, wp-settings.php, index.php, wp-load.php, and .htaccess files in your installation.
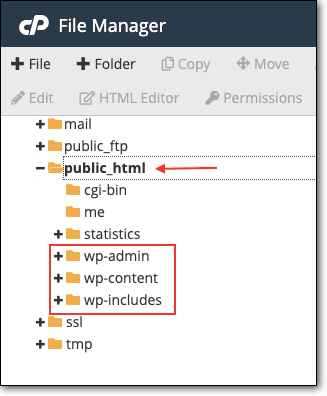
- Download a fresh copy of WP (with the same version as your installation) and then use the Diffchecker tool to manually compare your installed files with the new copy.
- Next, check for backdoors in your installation that hackers use to access your site even after you have cleaned it. For this, check for malicious PHP functions like eval, base64_decode, and gzinflate.
- The next step is to sign into the “Users” section of your dashboard and check for any suspicious or unknown Admin users. If found, then remove any such users.
- Apart from your core WP files, your installed plugins/themes can also contain malicious code. So, you need to compare each plugin or theme with its original copy, that you will need to download from their sites.
- The final step is to scan for any malware in your database. For this, you need to search for terms like <script>, eval, base64_decode, or gzinflate in your database tables.
A note of caution before we go – this method is fairly technical and complicated and requires you to modify critical Core WP files and database tables.
Conclusion
Hackers are constantly innovating and you’ll always find newer and more advanced forms of WordPress Hacked Redirect – that cannot be detected manually.
While there are many security steps that you can take to protect your website, installing a security plugin is the best investment you can make to keep your site secure. In the long term, it is certainly worth the time and effort saved, not to mention the peace of mind it provides. Or, you could invest in a WordPress maintenance plan like ours.
We hope you found this article to be informative and useful. Do share your thoughts and views with us regarding this article. Look forward to hearing from you.
Leave a Reply